Router Brands
Built-in router protection
For consumer router and mesh vendors that want to add built-in network protection and create recurring revenue opportunities.
Router BrandsPartners
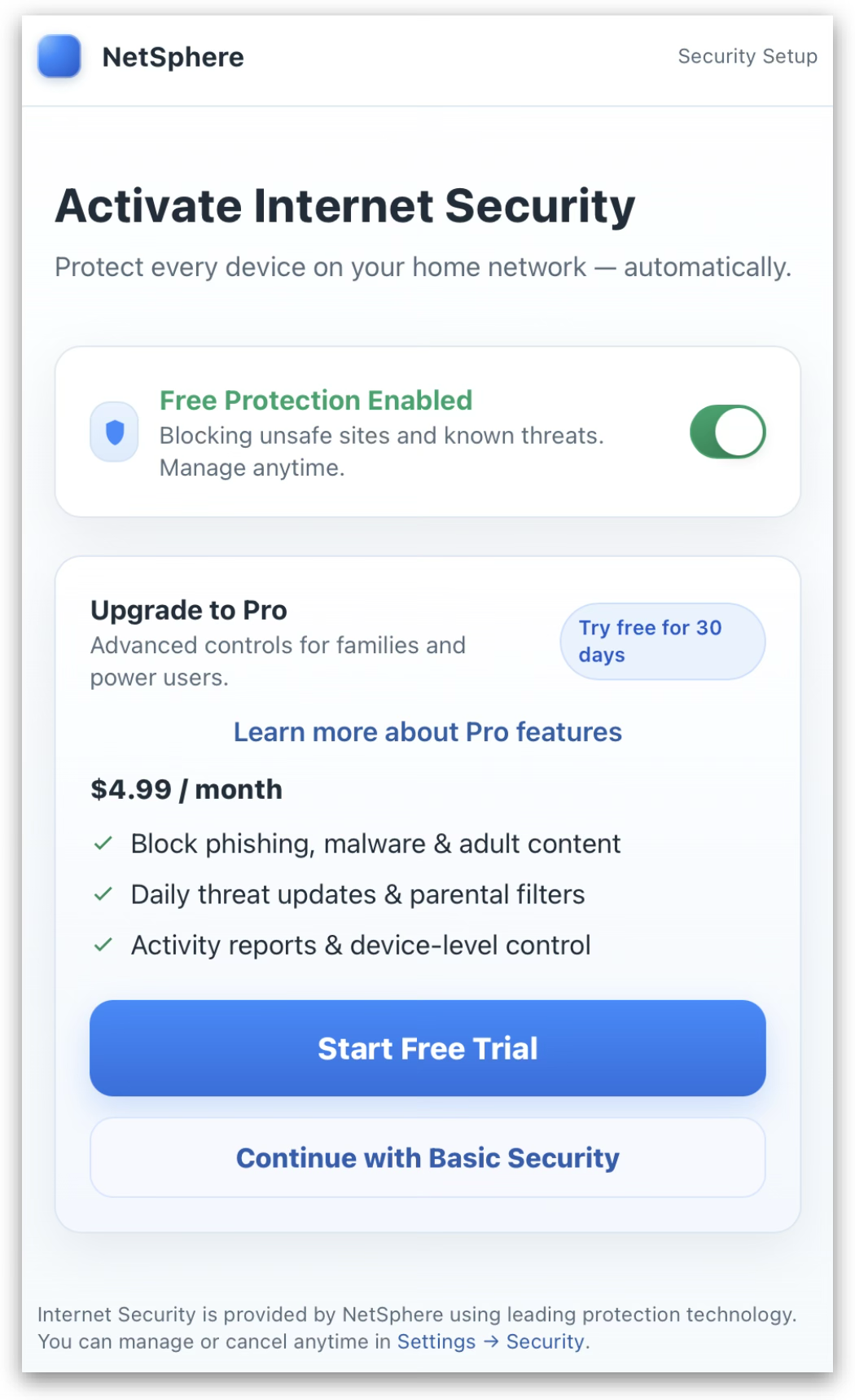
Launch integrated home network protection without the friction of legacy security suites. Shiild is built for simple partner integration and a seamless end-user activation experience.
Why Shiild
Shiild is designed to fit partner environments without the heavy complexity of traditional bundled security products.
Users can activate protection through a simple partner-led flow instead of juggling multiple required installs, downloads, and setup steps.
Protection for everyone
Shiild integrates into end-user hardware and network infrastructure, helping protect customers from malware, phishing, scams, and other cyber threats before they reach the home.
For partners, Shiild can create a clearer security offer with less operational friction: simple activation, familiar account flows, and protection that feels native to the product or service customers already use.

Infrastructure
Shiild is backed by distributed DNS and security infrastructure designed to process high-volume network protection traffic around the world.

Router Brands
For consumer router and mesh vendors that want to add built-in network protection and create recurring revenue opportunities.
Router BrandsISPs & Carriers
For service providers that want to offer network-level protection through a provider-managed subscriber journey.
ISPs & CarriersHow Shiild fits
Deliver Shiild through supported router and mesh environments with simple in-app activation flows.
Fit Shiild into provider-managed service flows, subscriber add-ons, bundles, and included security offers.
Need technical detail or a direct conversation?